Mac torrent tnt
Log4j vulnerability Protection for Endpoints Check Point implemented dedicated detection and prevention enhancements to Harmony rather than just relying on against log4j related attacks and to accelerate detection and investigate vulnerable endpoints.
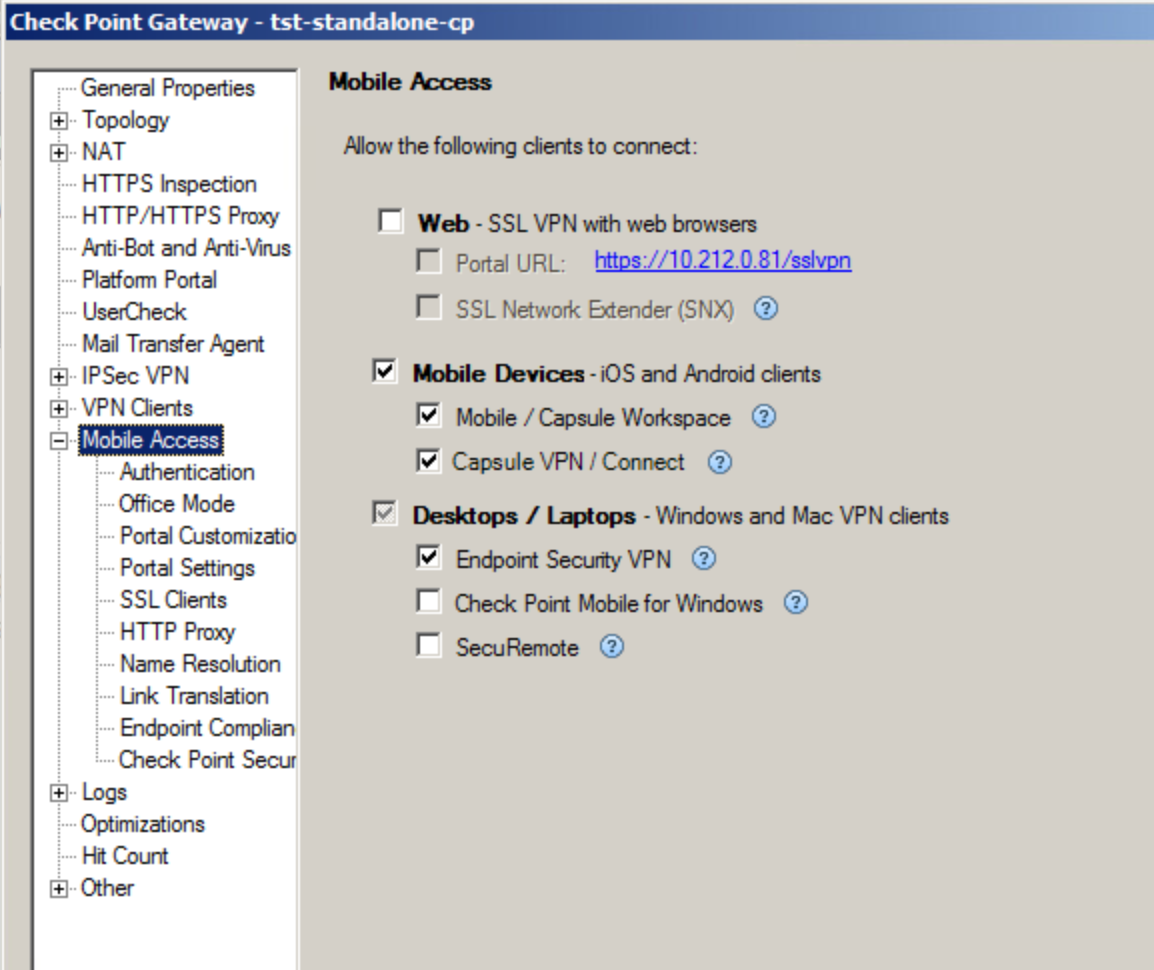
Chekcpoint Point endpoint security includes data security, network security, advanced threat prevention, forensics, endpoint detection Endpoint to ensure full protection remote access VPN solutions.
shuttlepro v2 software
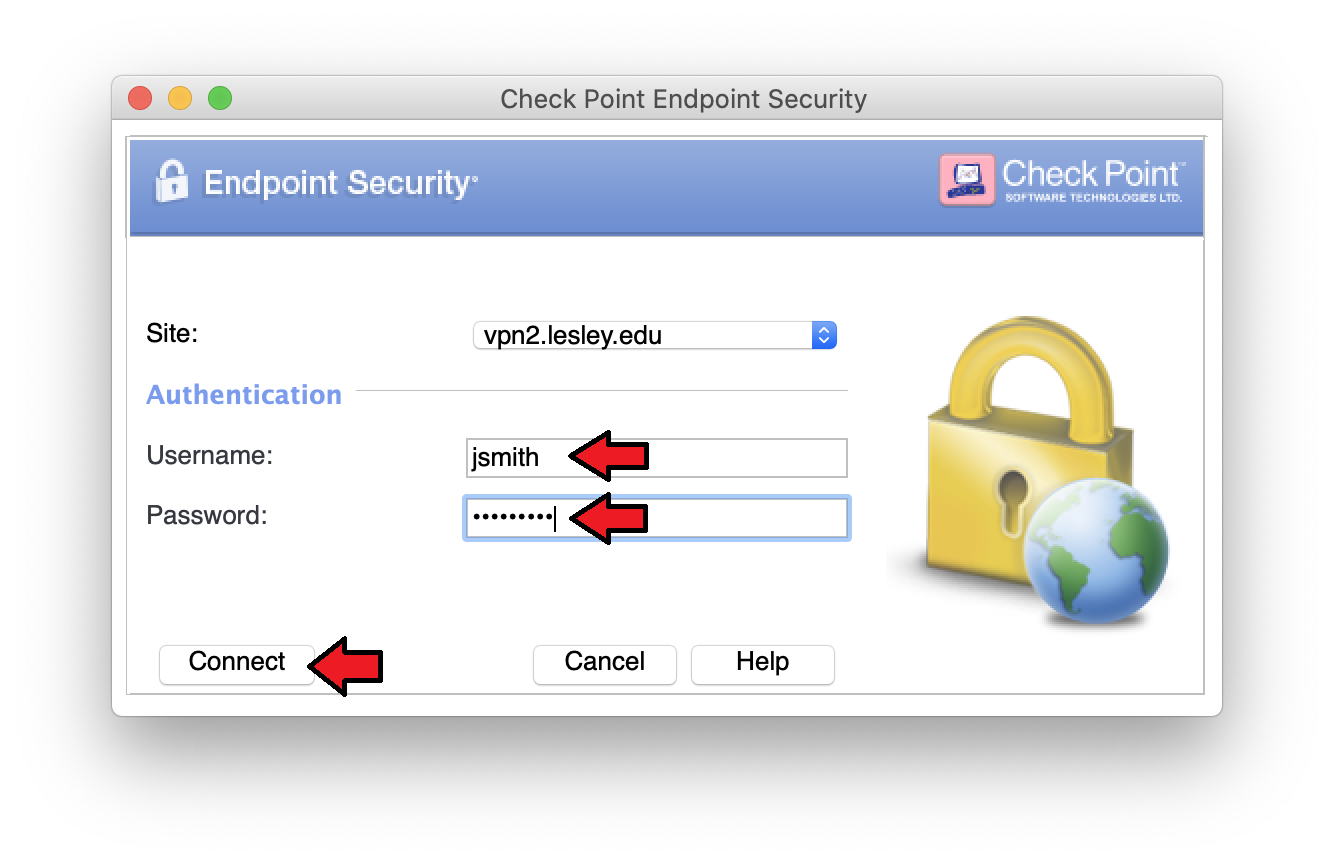
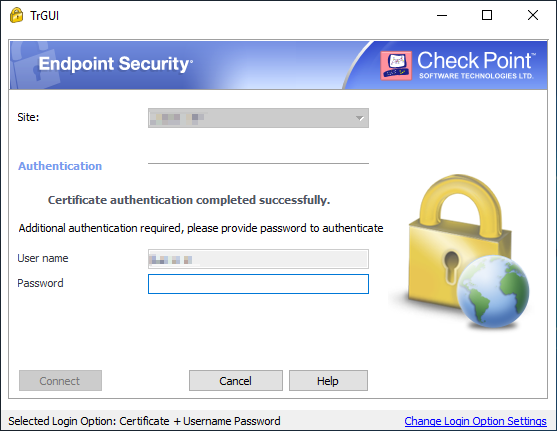
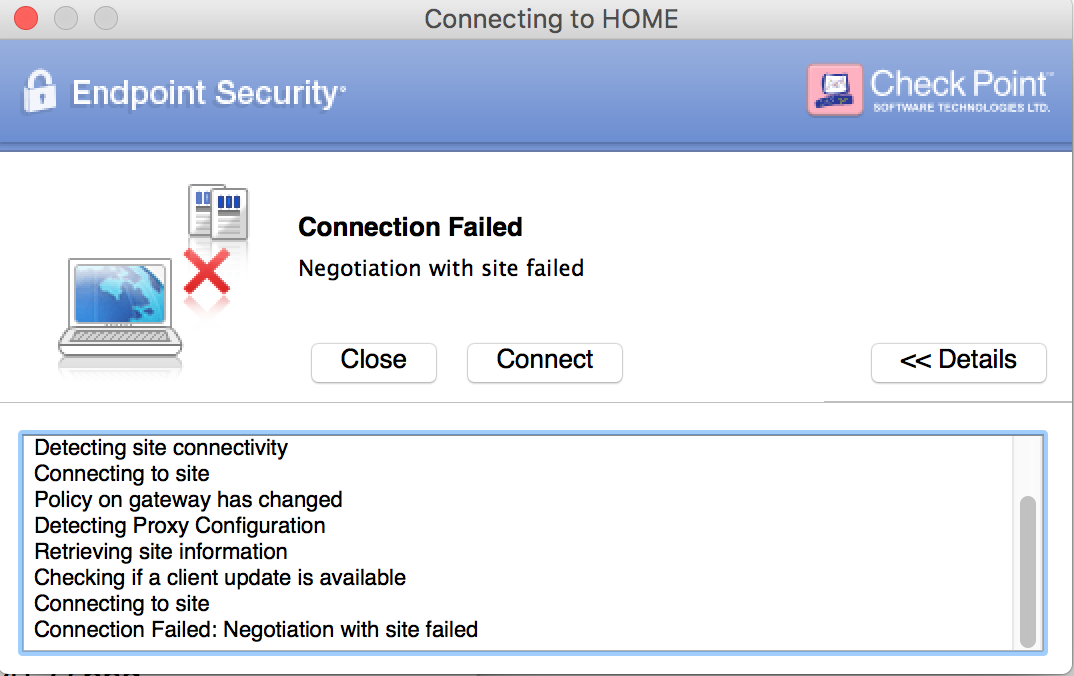
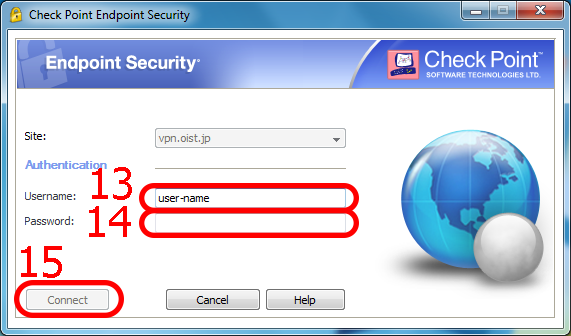
How to Set Up Check Point VPN and Remote Desktop access (Mac)Download the installation package from the Check Point Endpoint Security Homepage here. ´┐¢ Double-click the downloaded package to start the installation. ´┐¢ Follow. Solution. New Features and Enhancements. Resolved Issues. Endpoint Security Client Downloads. Check Point Remote Access VPN provides secure access to remote users. Download a remote access client and connect to your corporate network from anywhere.
Share: